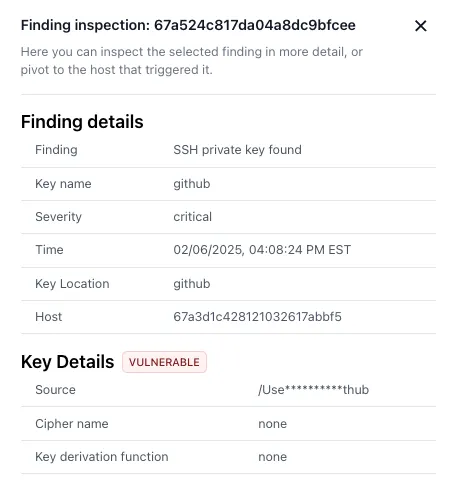
Discover
Know what you're running before someone else finds out. NovaCove surfaces shadow IT, misconfigured resources, and data exposures — prioritized by what would actually hurt.
- OAuth apps your team installed this week
- Cloud resources outside your known inventory
- Documents shared beyond their intended audience
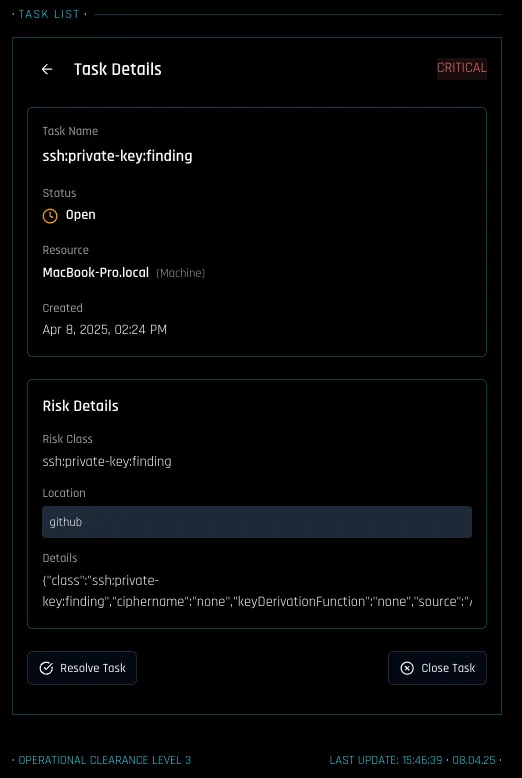
Protect
When you find something that needs fixing, fix it. One-click remediation for the common cases. Clear guidance for the rest. Controls matched to your maturity — not a one-size checklist.
- Revoke risky OAuth permissions directly
- Tighten document sharing with owner context
- Apply network security rules without guesswork
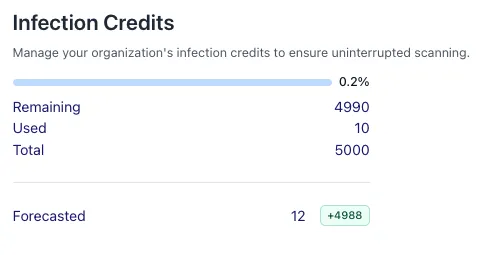
Prove
Hand your prospect a query endpoint, not a questionnaire. Your security posture is live and verifiable — because the evidence is a byproduct of how access actually works. And when you do want SOC 2 certification, the evidence is already collected.
- Live, queryable security posture — not a point-in-time PDF
- Pre-canned queries that replace the security questionnaire
- Evidence that maps to SOC 2 requirements if you later pursue certification